Updated (14th August 2020): for more information on this project, read Vincent’s blog post here
One of the most fascinating aspects of working for a company like VMware is the opportunity to work directly with the product teams who design and build the solutions I get to play with.
But at the rate the company is making acquisitions or releasing products, it’s actually a constant challenge to keep all the various VMware products not only compatible but as seamlessly integrated as possible.
I recently got involved in an interesting initiative with the Business Units (BUs) responsible for VMware Cloud on AWS and vRealize Automation (vRA) & vRealize Automation Cloud (vRA Cloud) to improve how we integrate these solutions together. I collected a fair amount of feedback from VMware colleagues and customers and reported back to the product teams. Based on the feedback, a number of initiatives kickstarted, such as:
- Let’s provide a high-level brief explaining the benefits of using both solutions together,
- Let’s publish step-by-step guides such as this one and this one,
- Let’s facilitate the installation and consumption of vRA Cloud for VMC customers, as described by Vincent in the following blog post.
One thing we didn’t have yet was the ability to create VMC SDDCs directly from vRA or to create networking and security constructs directly from the platform.
And this is what I have been working with Vincent Riccio (from our Cloud Management Business Unit): using Action-Based Extensibility (ABX) to consume and automate actions on VMware Cloud on AWS. For example, with the prototype below, we can now launch SDDCs straight from a vRA Service Broker Catalog!
In our scenario, we are going to leverage a lot of the Python scripts I created in a previous project (Python Client for VMware Cloud on AWS).
For example, here is how we can create a VMC network from a vRA Catalog. We’ll be using some Python but you don’t actually have to know any Python to use it.
First, make your way to vRealize Cloud Assembly, where we will create a number of Actions (such as creating a network) that we can publish on the catalog for the end-users to access:
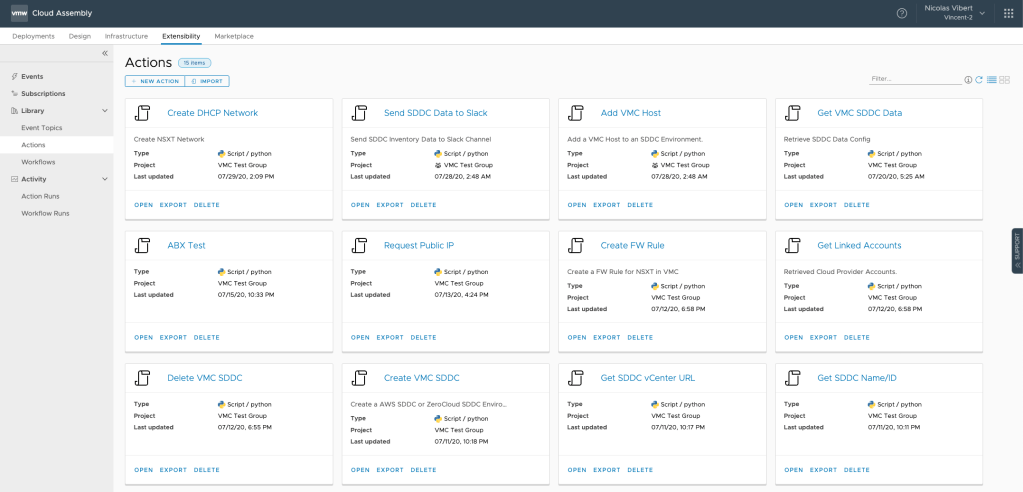
Check the Extensibility Tab and go to Library / Actions and we’ll define a new action. As you can see, we’ve been busy creating a ton of actions.
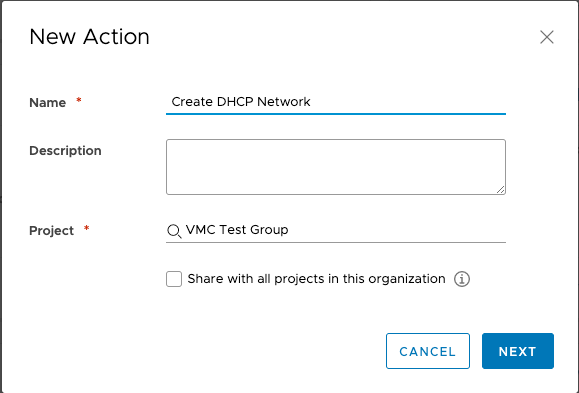
When you create a new action, you need to assign it to a project (which you would have defined earlier in Infrastructure / Administration).
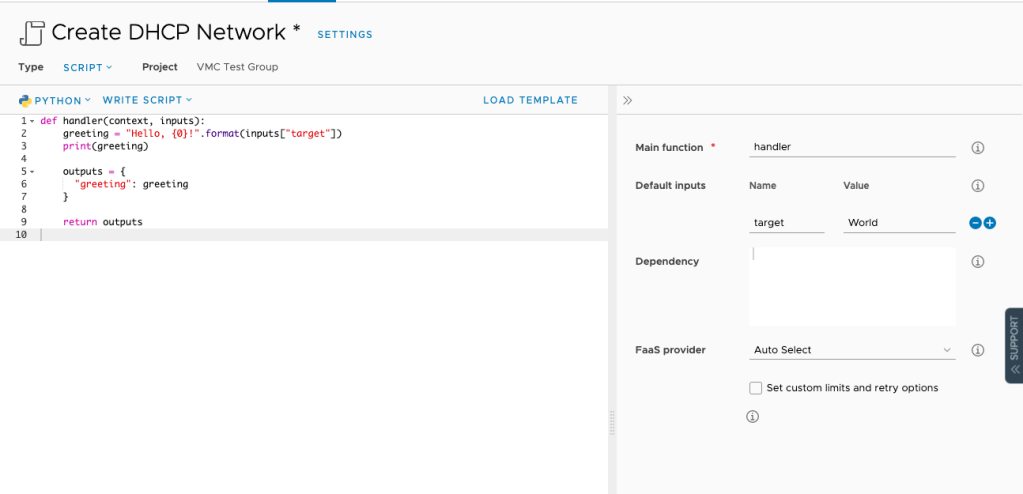
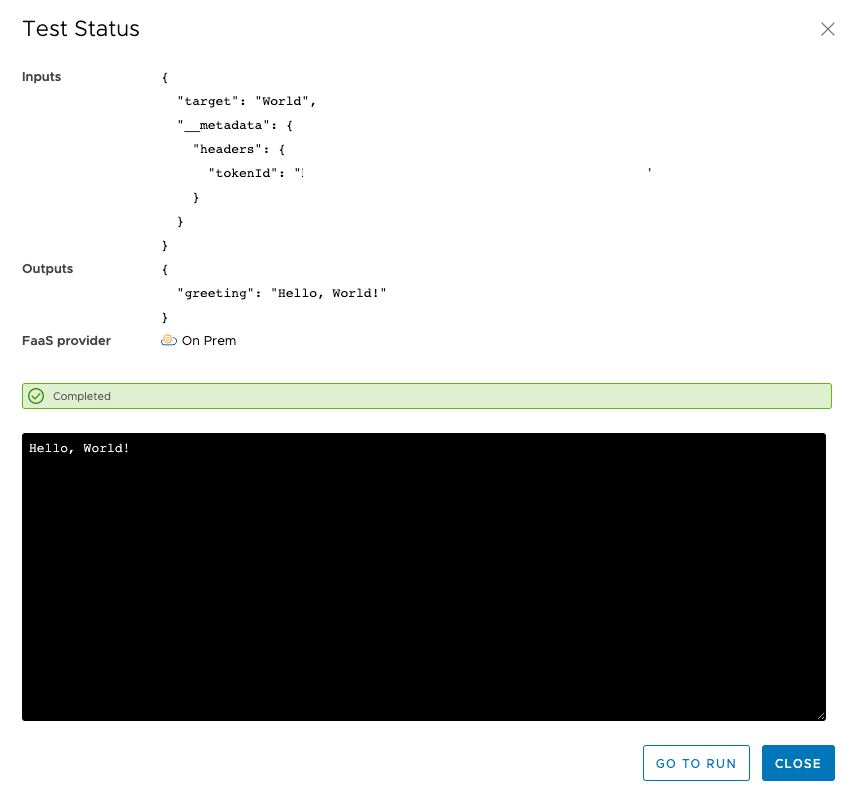
The default action below includes a “Hello World” Python script – when you save and test and check the test status, you will see that “Hello, World” has been printed:
Now, let’s remove the “Hello World” stuff and copy/paste the following code. Make sure you update the Refresh Token, SDDC Id and Org Id accordingly.
import requests # need this for Get/Post/Delete
import json
strProdURL = "https://vmc.vmware.com"
def getAccessToken(myKey):
params = {'refresh_token': myKey}
headers = {'Content-Type': 'application/json'}
response = requests.post('https://console.cloud.vmware.com/csp/gateway/am/api/auth/api-tokens/authorize', params=params, headers=headers)
jsonResponse = response.json()
access_token = jsonResponse['access_token']
return access_token
def getNSXTproxy(org_id, sddc_id, sessiontoken):
""" Gets the Reverse Proxy URL """
myHeader = {'csp-auth-token': sessiontoken}
myURL = "{}/vmc/api/orgs/{}/sddcs/{}".format(strProdURL,org_id, sddc_id)
response = requests.get(myURL, headers=myHeader)
json_response = response.json()
proxy_url = json_response['resource_config']['nsx_api_public_endpoint_url']
return proxy_url
def newSDDCnetworks(proxy_url, sessiontoken, display_name, gateway_address, dhcp_range, domain_name, routing_type):
""" Creates a new SDDC Network. L2 VPN networks are not currently supported. """
myHeader = {"Content-Type": "application/json","Accept": "application/json", 'csp-auth-token': sessiontoken}
myURL = (proxy_url + "/policy/api/v1/infra/tier-1s/cgw/segments/" + display_name)
json_data = {
"subnets":[{"dhcp_ranges":[dhcp_range],
"gateway_address":gateway_address}],
"type":routing_type,
"display_name":display_name,
"domain_name":domain_name,
"advanced_config":{"connectivity":"ON"},
"id":display_name
}
response = requests.put(myURL, headers=myHeader, json=json_data)
json_response_status_code = response.status_code
if json_response_status_code == 200 :
print("The network " + display_name + " has been created.")
else :
print("There was an error. Try again.")
return
Refresh_Token = "XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX"
ORG_ID = "XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX"
SDDC_ID = "XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX"
def handler(context, inputs):
print('Create Network')
display_name = inputs["Name"]
gateway_address = inputs["Gateway"]
dhcp_range = inputs["Range"]
routing_type = inputs["Type"]
domain_name = inputs["Domain name"]
session_token = getAccessToken(Refresh_Token)
proxy = getNSXTproxy(ORG_ID, SDDC_ID, session_token)
newSDDC = newSDDCnetworks(proxy, session_token, display_name, gateway_address, dhcp_range, domain_name, routing_type)
print(newSDDC)
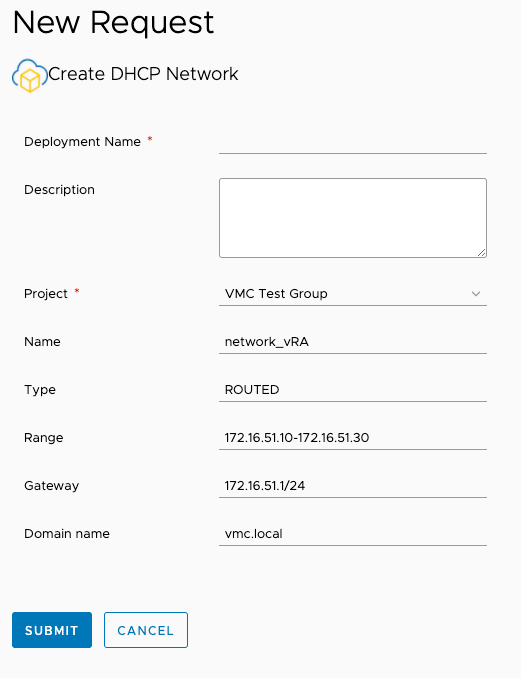
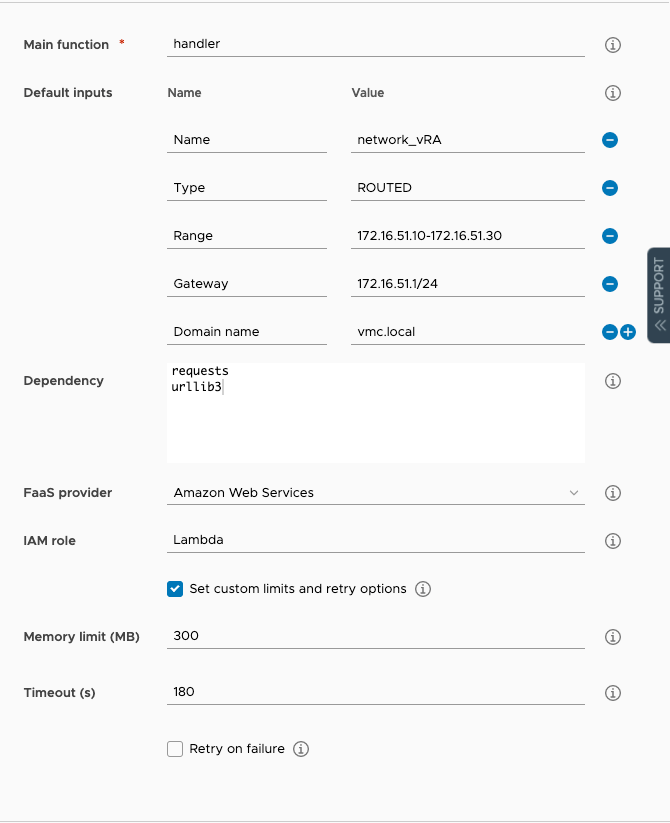
On the right-hand side, add a number of default inputs. These will be presented to the end-user on the catalog. These are the default values that are also used when you click on “TEST”.
As you can see, the script will be executed via AWS Lambda. The instructions here explain how to set Lambda all up.
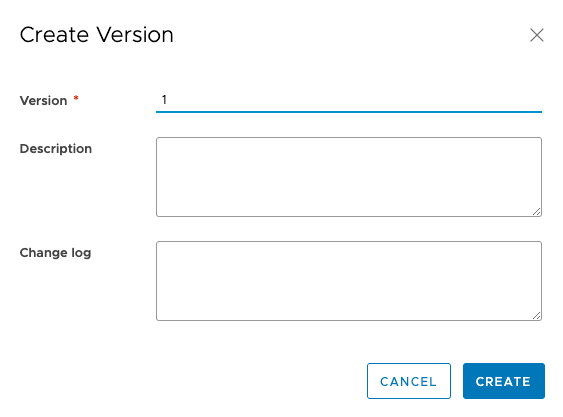
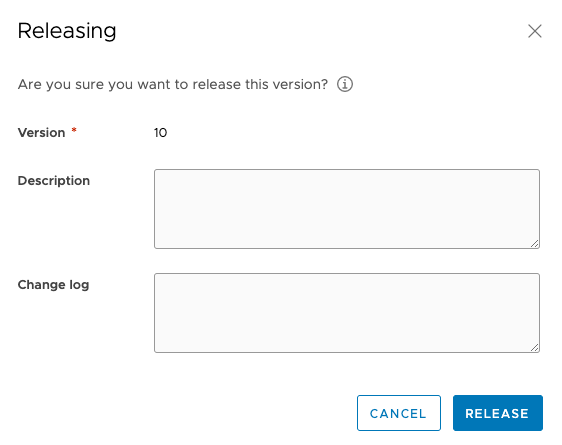
Once you created a version and released it…
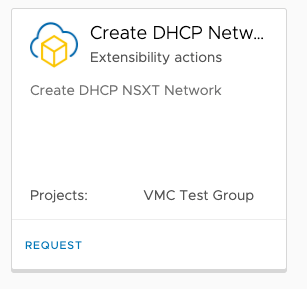
…it will appear on the Service Broker Catalog:
The end-user can request a network:
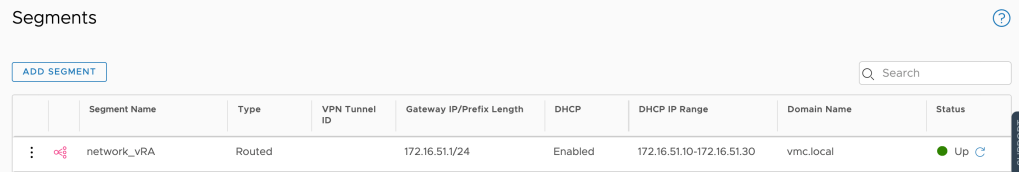
As soon as you submit, you will see the new network being created in VMware Cloud on AWS:
Here are some of the actions we have already published on GitHub:
- Create a network
- Add a host
- Request a public IP
- Create a CGW security rule
More will be published, depending on customer feedback and demand. Please contact me or raise requests on GitHub and we’ll update it accordingly.
Thanks for reading!

3 thoughts on “Automation with VMware Cloud on AWS and vRealize Automation ABX”