This short post describes one of the options to connect VMware Cloud on AWS to an on-premises DC: the NSX L2VPN.
For customers that need to maintain the same IP addresses after they’ve migrated workloads to VMware Cloud on AWS, they can use the NSX Layer 2 VPN functionality.
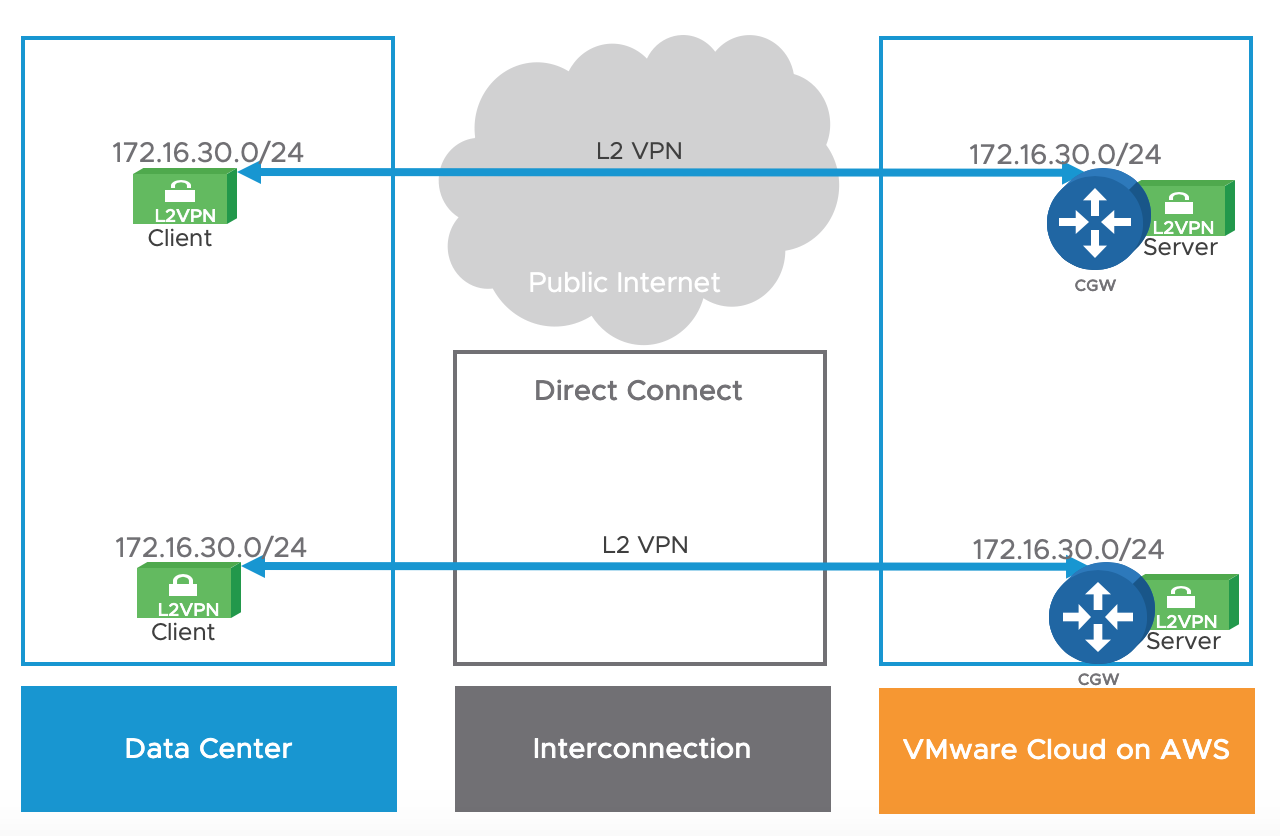
This option can be leveraged over the public Internet or a private Direct Connect circuit.
NSX has offered a L2VPN capability for several years. A L2VPN enables customers to stretch networks between two different sites, over a public or private network (with no requirements on MTU).
VMware Cloud on AWS uses NSX to provide L2VPN features in your cloud SDDC.
L2VPN is used to extend Virtual Machine networks.
The L2VPN is independent of the VMkernel networks used for migration traffic (ESXi management or vMotion), which use either a separate IPsec VPN or a Direct Connect connection.

An L2VPN can extend up to 25 of your on-premises networks.
The L2VPN is based on a L2VPN client and a L2VPN server. The L2VPN Server is located within VMware Cloud on AWS while the L2VPN Client can either a NSX Edge Client if a customer already runs NSX on-premises or the “Standalone Edge Client” (deployable with an OVA).
Note that you don’t need to own NSX licenses in order to run the ‘standalone edge client’ – it is free to download on my.vmware.com

The L2VPN traffic is transported in GRE over IPSEC in the NSX-T Release (SSL/TCP in the previous NSX-V release).

6 thoughts on “NSX L2VPN”